Common UcaaS Questions and Answers
A unified communications solution is often the first step for organizations looking for ways to increase flexibility and resilience with cloud technology. With UCaaS, teams can stay productive, engaged, and connected, whether they are working from home, in the office, or on the go. However, before adopting any new technology, it’s important to learn as much as you can about how it works, what it can and cannot do, and potential challenges. We’ve put together this list of UCaaS questions and answers to help you start the research process.
What Is UCaaS?
UCaaS, or unified communications as a service, is a cloud communications solution that offers all the main types of business communications from one platform.
What Features Are Included?
This can vary a lot between cloud providers, so be sure to do your homework and ensure the platform you use has everything you need. Often, UCaaS comes with video, voice, chat, and file sharing,
You’ll also want to look at the more granular details such as advanced voice features like voicemail, call waiting, and caller ID, as well as a contact center solution to power your customer success. Other details to look for include rich video conferencing features, including interactive presentation tools, screen sharing, and HD video, and a real-time backup and restore function for your file management.
What Do Users Need to Access the Technology?
As a cloud solution, users simply need to download the application to their device and log in to the platform to get started. Your employees can chat with co-workers, launch video meetings, share files, and more from any location as long as they have an internet connection.
The software is hosted on secure off-site servers, so there’s no need for on-site hardware or extra IT resources to manage and maintain the technology. You can, however, purchase specific hardware such as desk phones, headsets, and webcams to work with your technology.
Does My Company Need a New Phone System to Make UCaaS Work?
UCaaS relies on VoIP (voice over internet protocol) technology. This means voice data is transmitted over the internet, so there’s no need to have a traditional phone line to make and receive calls. In fact, this is one of the largest draws of cloud phone systems – your business can likely save on your phone bill by switching from a traditional phone system to VoIP technology.
Can Employees Use Desk Phones Through the UC Platform?
Yes, they can! You can use feature-rich desk VoIP phones to make and receive calls, send messages, and more, all through the same unified communications app you have on your computer, mobile phone, or other devices. These desk phones are plug-and-play so that you can set them up yourself right away.
Is Communicating Through a UC App Secure?
As with any cloud technology, security can be a big concern. To ensure your teams can use your UCaaS solution confidently, it is important to inquire about the security practices your cloud provider uses.
Your provider should be able to explain how they offer a worry-free experience. Here are some of the security best practices to expect from your cloud services provider:
- Third-party audits to validate their security controls
- Adherence to all applicable compliance standards such as HIPAA and PCI-DSS
- Advanced encryption for email services
- Ongoing network monitoring and detection
- Highly secure data centers with security guards, controlled access, and 24/7 monitoring
- Rigorous background checks for employees
How Reliable Is UCaaS?
Reliability is critical. If your software doesn’t work for your teams, you could have problems with productivity and employee frustration. To ensure the UCaaS solution you adopt will perform, look for at least 99.99% service reliability and accessible technical support.
How Much Does UCaaS Cost?
One of the huge benefits of UCaaS technology is its affordability. Because it uses a subscription-based payment model, there’s no need to make a large IT investment to get started. You pay for the number of users you need.
You can also scale up or down by adding or subtracting users. To enjoy the cost-efficiency benefits, look for a provider that offers transparent, flexible pricing and doesn’t require a contract.
Start Benefiting with a Leading UCaaS Solution
Whether you want to save money with cloud-based communications, unlock your teams’ potential, boost resilience, or all of the above, UCaaS can be game-changing for businesses. YeoVoice, powered by Elevate, is a comprehensive unified communications platform that comes with all the features your business needs to thrive. Reach out to our team today for a quote.
Information used in this article was provided by our partners at Intermedia.
It’s something many people admit to doing: They reuse the same password across a few different services.
We are not judging you if you’ve done it – it’s easy to see why thousands of people do this every day. It feels like an easy way to get signed up for something. If you reuse a password, you won’t have to go through the hassle of remembering it and needing to reset the password in the future.
However, you only have to do this once, and you’re at considerable risk of something called credential stuffing.
This is where hackers get hold of millions of usernames and passwords. These typically come from the big leaks we hear about in the news.
And then, they try all those details to see if they can log in to other digital services. They use bots to stuff the credentials into the login box, hence the name.
Because it’s automated, they can sit back until their software manages to log in to an account, and then they can do damage or steal money.
Stats suggest that 0.1% of breached credentials will result in a successful login to another service.
The best way to protect yourself against this kind of attack is to never, ever reuse passwords.
Use a password manager to generate long, random passwords, remember them for you, and auto-fill them. The less hassle for you, the less likely you are to reuse a password. Consider giving a password manager to each of your staff as well.
And if you know you have reused passwords in the past, you should change all your passwords on all active services just to be safe.
Running a business can be challenging. With numerous tasks to juggle, from communicating with marketing or finance teams to hiring staff, getting everything done can take a lot of time.
In recent research by Plum Consulting and Sage, businesses estimated they lost 71 days each year to admin. That’s 14 working weeks doing nothing but admin.
Your staff process paperwork for a variety of reasons. So, for your business, how do you go about cutting back on this workload?
8 tips to reduce time spent on processing paperwork
1. Look at software
Several software options are available to help you cut back on admin, but they need to work for you, and you need to use them. Try them and see what works and what does not. They are likely to include CRM and accounting systems, so take your time and work out which one will work best for your business.
2. Try outsourcing
You don’t have to be the expert on all things.
It is always more profitable to gain sales than focus on administrative tasks, so you could look at outsourcing some of your admin. Make sure you outsource to the right provider – a complete business support service might be just what you need.
A business such as this will offer a wide range of services that you can tap into as you need them or provide a full back office that effectively runs the admin for your company.
3. Prioritize your work
Make sure you prioritize your tasks each day so you do the most profitable or productive things first.
4. Be aware of the time taken on admin
Track the time it takes you to do your administrative tasks over a month or so. It will probably be more than you think.
5. Spend some time on templates
Spend a little time building a bank of templates that you can tap into each time you need to contact a customer. These could include your letterheads, your quotes, invoices, and receipts.
6. Make sure your processes are in place
Decide how you will manage your late payers and invest in credit control activities.
7. Make sure you are contactable
Nothing puts a potential customer off faster than not being able to get hold of you. Think about investing in a telephone answering service, so not only do your customers get a personal service, you’re aware of who you need to contact and why.
8. Keep on top of your accounts
Regular time spent on keeping your accounts up to date pays off hugely in the long run. Get into a habit of putting receipts into one place to find them when you need them. Even better, with the right accounting solution, you can scan them with your mobile phone, and the info will appear in your software.
Getting started with reducing paperwork
Processing paperwork can be time-consuming and slow down the day-to-day running of your business. Although some paperwork is necessary, it’s essential to embrace the digital age and use AI or OCR to help with invoicing, receipts, or file storage.
Looking to invest in software that can cut down your admin time? Contact Yeo & Yeo Technology.
Information used in this article was provided by our partners at Sage.
Enterprise Resource Planning (ERP) is a desirable proposition for businesses looking to consolidate management information and disperse it throughout the company. Yet, an economic case has to be made to justify the investment.
Both capital and operational expenditures must be compared to the expected return on investment (ROI). Where the projected ROI exceeds the total cost of ownership (TCO), introducing a new ERP system should positively impact profitability. Still, there are several considerations to be made before one can arrive at that conclusion.
What are the costs of an ERP system?
Businesses need to consider acquisition expenses and the costs associated with deploying ERP across the workforce. These costs can include:
- Capital resources used to fit the solution to new business models
- Time to integrate existing and new technologies, including converting files and consolidating management information.
- Routine testing, periodic ERP reviews, and upgrades, which may be required over time.
- Training to help team members adapt to new procedures.
What are the benefits of an ERP system?
ERP purchases should be considered a long-term purchase, so it is essential to consider the benefits it will bring to the business, including:
- Streamlined resource management processes, which simplify procedures, reduce re-work and decrease manual handling costs.
- The automation of manual tasks, which increases the speed of the delivery and reduces human error. Key workers can then focus on value-adding tasks, with reliability ensured thanks to all-encompassing systems which flag up inaccuracies and mistakes.
The most commonly cited advantage of using ERP systems is that it gets all business functions moving together. ERP systems make it simpler to record and report data across a range of tangibles, making monitoring business processes easier and troubleshooting instantaneous. With precise data in the hands of decision-makers, organizations can set realistic expectations in terms of timescales and costs.
Setting reasonable expectations
ERP systems won’t change business performance overnight, and they are in many ways an enabler of change rather than the remedy. It makes sense to be conservative when projecting the economic benefits of new ERP systems and processes, as unrealistic goals can significantly impact the perceived success of the implementation.
Working out a ‘worst case’ cost scenario, along with a ‘likely’ estimate, is advisable for businesses, but establishing a sound business case for investment in ERP is equally as important, particularly in a tough economic climate with budgets remaining constrained. This gives project goals a strategic context, making it easier for executives to decide whether to opt for ERP.
Information used in this article was provided by our partners at Sage.
With more of us working remotely now, coffee shops are getting busier again as we look for somewhere other than home to work.
But while going to a coffee shop can be great for getting rid of distractions, it’s not so good for security.
That’s because public Wi-Fi is a hotspot for data theft. Any data sent over public Wi-Fi that doesn’t need a password to access is vulnerable to theft or manipulation from someone else using that network.
And it’s not just other Wi-Fi traffic you need to consider. There are also fake networks to be wary of. You think you’re connecting to the coffee shop’s Wi-Fi … but how do you know it isn’t a phony version with the same name?
As soon as you log on, they can suck up all your credentials and any other personal data on your device.
If your team uses public Wi-Fi regularly, the best practice is to use a VPN (Virtual Private Network) to keep your data safe.
What is a VPN?
A VPN is a service that encrypts all of a device’s internet traffic and routes it through an intermediary server in a location of the user’s choosing. A VPN grants numerous benefits to users and is particularly useful to people who use public Wi-Fi while traveling for work or fun.
Anyone who happens to intercept internet traffic between the smartphone or laptop and the VPN server won’t be able to decipher its contents, including Wi-Fi hackers.
Dishonest individuals are continually finding clever new ways to exploit technology for their personal gain. As always, think before you connect to keep your data safe.
Information used in this article was provided by our partners at MSP Marketing Edge.
Boost Productivity, Save Time, and Improve Customer Experience
Increasing productivity in your business can be tricky.
We like to think our loyal team is working hard and using time wisely. And realistically, many of your people will be doing just that. But just because everyone is working hard doesn’t mean you’re not still wasting time.
Think about your average week. How long do you or your people spend logging information when you’ve spoken to clients or taken on new business?
How many emails or calls does it take to arrange a meeting at a time to suit everyone?
And how about the time you spend creating presentations and fiddling around looking for suitable images, then finding the right place to put them in the slides?
All these little things add up. And as well as being time wasters, they’re probably causing a lot of frustration too. That can lead to demotivated employees.
Fortunately, Microsoft 365 offers numerous in-suite apps to help you cut down or remove much of this wasted time. And to give your team a motivational boost because their work lives have been made easier.
Learn more about the top 10 Microsoft productivity apps in our free eBook.
Years ago, it may have seemed like only government agencies with top-secret intel or wealthy international banks had to worry about hackers. Nowadays, even the smallest small business could see its reputation ruined by a data breach, while larger companies could have their sensitive data taken hostage in a ransomware attack that costs millions to resolve.
A cybersecurity assessment can help ensure that your business is taking the proper steps to protect itself. It can also give you a competitive edge by demonstrating to customers and prospects that you take data privacy seriously.
More tech, more risk
Many, if not most, of today’s companies are taking advantage of technologies that allow them to gather, track and analyze customer and financial data. This includes software for mission-critical activities such as payroll, accounts receivable and payable, supply chain management, HR and benefits, and on-site security.
These systems are often cloud-based, meaning the information is stored online so users can access it remotely at any time of day or night. The convenience and analytical power are breathtaking, but they also create a tempting target for cybercriminals and raise the stakes of exposure exponentially.
In truth, the risk of a breach goes far beyond disclosure of confidential personal or financial information. It also raises serious concerns about potential personal injuries, property damage and work stoppage. Imagine the harm a hacker could cause by tampering with a building’s security or fire systems, or remotely manipulating vehicles or equipment.
Benefits of an assessment
Conducting a formal cybersecurity assessment helps you:
- Take inventory of your hardware and software,
- Identify potential vulnerabilities (including access by vendors, partners, and current and former employees), and
- Implement internal controls and other protections to reduce risk.
An assessment can also enable you to develop an incident response plan to mitigate the damage in the event of a breach.
There are several recognized cybersecurity standards and frameworks available to guide these efforts, including those developed by the National Institute of Standards and Technology and the International Organization for Standardization. The U.S. Small Business Administration also offers cybersecurity assessment tips and best practices on its website.
If you’re particularly concerned, you might want to shop around for a qualified IT consultant to conduct a customized risk assessment. This may make sense if you’re in an industry subject to specific risks.
Become a hard target
Cybersecurity is important for every size and type of company. It may be comforting to think that the bad guys only go after the big guys, but hackers don’t always go after businesses with deep pockets. Sometimes they attack the softest target. Make sure you’re well-protected.
© 2021
You know that feeling when you look in your phone’s app store, and 29 apps are asking to be updated? Yes, everyone gets annoyed with this sometimes.
What’s worse is when you’re working on your computer, and software pings up a message saying it needs to be updated. At least phone apps don’t take long and don’t interrupt you that much. On your computer, it’s too easy to hit “remind me later” and forget it.
Often these updates are known as patches. And they’re there to keep your business safe.
When a vulnerability is found in software or an operating system, the developers work fast to create a minor patch that fixes the vulnerability. This is like a Band-Aid until a full update is created.
It’s risky to ignore any updates. A recent study found that today’s top 4 most exploited vulnerabilities were discovered between 2018 and 2020.
The fact that they’re still in the top 4 shows that many businesses are skipping updates!
The answer is simple: Get your IT partner to make sure all your software is always up to date. This can be done remotely and efficiently with minimal disruption to you and your team.
Yeo & Yeo Technology’s YeoCare Managed Services are designed to keep your network healthy and detect failures before they happen. Learn more about how YeoCare can help protect your organization.
Information used in this article was provided by our partners at MSP Marketing Edge.
Can I take a screenshot in Windows 10?
Yes! The easiest way to capture and save a copy of your entire screen is to hit the Windows key + Print Screen key. Your picture will be saved to the Pictures > Screenshots folder.
How can I see how much storage space my apps are taking up?
Sometimes if your computer is running slowly, it’s a good idea to remove some apps you no longer use. To see how much storage space they’re taking up, go to Settings > System > Storage. Then look at the drive you want to search (This PC, for example) and click Apps & Games.
Can I get rid of the ads on my Start menu?
Yep! Go to Settings > Personalization > Start. Then turn off Occasionally show suggestions in the Start toggle switch.
The COVID-19 pandemic forced many businesses to rely more heavily on technology. Some companies fared better than others.
Many businesses that had been taking an informal approach to IT strategy discovered their systems weren’t as robust and scalable as they’d hoped. Some may have lost ground competitively as fires were put out and employees got back up to speed in an altered working environment.
To keep your approach to technology relevant, you’ve got to regularly reassess processes and assets. Here are six questions you should ask when evaluating your technology and considering upgrades.
- What are our users saying?Every successful IT strategy is built on a foundation of user feedback. Talk with (or survey) your employees about what’s happened over the last few months from a technology perspective. Find out what’s working, what isn’t and why.
- Do we have information silos?Most companies today use multiple applications. If these solutions can’t “talk” to each other, you may suffer from information silos — when different people and teams keep data to themselves. Shifting to a more remote workforce may have worsened this problem or made it more obvious. If it’s happening, determine how to integrate critical systems.
- Do we have a digital file-sharing policy?Businesses used to generate tremendous amounts of paperwork. Sharing documents electronically is much more common now but, without a formal approach to file sharing, things can still get lost, or various versions of files can cause confusion. Implement (or improve) a digital file-sharing policy to better manage system access, network procedures and version control.
- Has our technology become outdated? Technology that may have been at least passable before the pandemic may now be falling far short of optimal functionality. Look closely at whether your business may need to upgrade hardware, software or platforms sooner than you previously anticipated.
- Do employees need more training?You may have implemented IT changes during the pandemic that employees haven’t fully understood or have adjusted to in problematic ways. Consider mandatory training and ongoing refresher sessions to ensure users take full advantage of available technology and follow proper procedures.
- Are your security protocols being followed?Changes made to facilitate remote or hybrid work may have exposed your systems and data to threats from disgruntled employees, outside hackers and ever-present viruses. Ensure you have a closely followed policy for critical actions such as regularly changing passwords, removing inactive users and installing security updates.
Technology has played a critical role in enabling businesses to stay connected internally, communicate with customers and remain operational during the pandemic. Our firm can help you assess your IT strategy in today’s economy and identify cost-effective process changes and budget-conscious asset upgrades.
© 2021
According to the FBI, people in the U.S. lost $133,400,000 to romance scams between January 1st and July 31st of 2021. The average amount lost per user was in the tens of thousands of dollars. Often, scammers trick the victims into thinking they’re investing in cryptocurrencies.
How Cryptocurrency Impersonation Works
“The scammer’s initial contact is typically made via dating apps and other social media sites,” the FBI says. “The scammer gains the confidence and trust of the victim—through establishing an online relationship—and then claims to know about cryptocurrency investment or trading opportunities that will result in substantial profits. The scammer directs the victim to a fraudulent website or application for an investment opportunity. After the victim has invested an initial amount on the platform and sees an alleged profit, the scammers allow the victim to withdraw a small amount of money, further gaining the victim’s trust.”
The FBI explains that once the scammer has a victim on the hook, they’ll keep coming up with more reasons for the victim to send them money.
“After the successful withdrawal, the scammer instructs the victim to invest larger amounts of money and often expresses the need to act fast,” the Bureau says. “When the victim is ready to withdraw funds again, the scammers create reasons why this cannot happen. The victim is informed of additional taxes, that fees need to be paid, or that the minimum account balance has not been met to allow a withdrawal. This entices the victim to provide additional funds. Sometimes, a ‘customer service group’ gets involved, which is also part of the scam. Victims are not able to withdraw any money, and the scammers most often stop communicating with the victim after they cease to send additional funds.”
The FBI offers the following advice to help people avoid falling for these scams:
- Never send money, trade, or invest per the advice of someone you have solely met online.
- Do not disclose your current financial status to unknown and untrusted individuals.
- Do not provide your banking information, Social Security Number, copies of your identification or passport, or any other sensitive information to anyone online or to a site you do not know is legitimate.
- If an online investment or trading site promotes unbelievable profits, it is most likely that—unbelievable.
- Be cautious of individuals who claim to have exclusive investment opportunities and urge you to act fast.
Protect yourself and your employees from cryptocurrency impersonation and other social engineering scams with Security Awareness Training.
Information used in this article was provided by our partners at KnowBe4.
Which Dr. Seuss character are you? Who will be your Valentine’s Day date? Only a true genius will score 100 percent on this quiz.
Social media quizzes asking for personal information take advantage of an individual’s willingness to share and could be used to establish passwords, password hints, and more.
Think twice before taking that Facebook quiz!
 We’ve all seen them – quizzes on Facebook asking everything from which Harry Potter character are you, to what state you were born in, to your first pet’s name.
We’ve all seen them – quizzes on Facebook asking everything from which Harry Potter character are you, to what state you were born in, to your first pet’s name.
It seems that none of the people answering these questions saw the scene in the movie Now You See Me, where the main characters tricked Arthur Tressler into divulging personal information to be used later against him.
According to security vendor Avast, the new wave of social media quizzes may very well intend to do the same thing. “They’re meant to seem so light and fluffy that anyone looking for a boredom-killer might be amused by them. And that’s the point. The creators of these quizzes want them to appear meaningless and harmless. They want everyone to engage whimsically with them. Because in truth, many are phishing attempts at your data.”
Because of the seemingly innocent (and entertaining) nature of the quizzes, threat actors using such tactics can easily capture information that is often used as the source of passwords or password reset questions.
Don’t get hacked by social media phishing attacks
Many of your users are active on Facebook, LinkedIn, and Twitter. Cybercriminals use these platforms to scrape profile information of your users and organization to create targeted spear-phishing campaigns in an attempt to hijack accounts, damage your organization’s reputation, or gain access to your network.
Security Awareness Training can keep employees vigilant against such social engineering tactics, helping to minimize your organization’s threat surface and keep attacks from being successful.
Looking to educate your human firewall? Contact Yeo & Yeo Technology.
Information used in this article was provided by our partners at KnowBe4.
Recognize Malware Before It’s Too Late
These days, hacking is a profession. And a very lucrative one for some. The internet has made it very easy to access hacking knowledge and powerful automated tools.
Anything that has been designed to steal your data or hurt your computer systems is called malware – for “malicious software.” Some kinds of malware are very difficult to recover from. It’s rarely as simple as deleting an infected file.
While it’s not realistic to protect your business from 100% of malware attacks (without completely crippling your staff’s ability to do their work freely), you can take measures to minimize the risks and increase awareness.
In this eBook, we examine the nine most common types of malware, including:
- Viruses
- Worms
- Trojans
- Ransomware
- Spyware
Does your business have the proper cybersecurity infrastructure to protect against malware? Contact Yeo & Yeo Technology to learn about our cybersecurity solutions.
The latest data reveals ransomware’s pervasiveness throughout every industry, size, and type of organization, confirming its place as the number one cyberthreat today.
New data from Fortinet’s 2021 Ransomware Survey Report shows just how prominent ransomware attacks are, and how organizations aren’t making the connection between the cyberattack and their users. First, a bit of data on the state of ransomware attacks. According to Fortinet:
- 67% of organizations have been a target of ransomware attacks
- 16% have been hit three or more times
- 96% feel at least moderately prepared (despite the percentage of attacks indicating otherwise)
So, organizations should take a look at why they are being hit so much, right?
- Nearly a third (32%) say there’s a lack of security awareness training
- 61% have user training – but as part of an incident response plan (after and not before)
- 58% of ransomware attacks in North America start with phishing a user
And most importantly:
- In the list of protection and defensive measures essential to secure against ransomware, nowhere to be found is security awareness training:
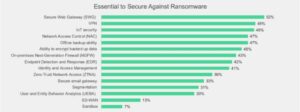
Source: Fortinet
We all need to do our part in preventing ransomware attacks. And that starts by building an effective ransomware strategy, including implementing proactive measures to educate your employees and stop cyberattacks.
It’s an action every organization needs to prioritize. Security awareness training can help create a forward-thinking security stance designed to prevent ransomware attacks that start with phishing as the initial attack vector. Learn more about the benefits of security awareness training now.
Information used in this article was provided by our partners at KnowBe4, and the article “Fortinet Ransomware Survey Shows Many Organizations Unprepared” from Fortinet.
Enabling enhanced productivity while driving down IT costs, cloud communications has been game-changing for manufacturers. Let’s look at the industry’s unique IT challenges and some of the surprising benefits this technology brings to the table.
IT Challenges in Manufacturing Today
From robotics to the internet of things (IoT), new technologies are pushing the industry forward exponentially. The problem is that rapid technological change can be out of reach for small and medium-sized manufacturing companies that won’t realize the cost-savings that come with large-scale operations. They may not have the resources to invest in new IT and develop solutions for leveraging data, analytics, and automation.
Cost-effectiveness is critical in manufacturing, but the reality is, investing in new technology is often expensive.
This is where cloud communications come in. It allows companies to dramatically reduce IT costs while making it far easier to manage operations. Manufacturers can streamline processes and collaborate using sophisticated data without increasing hardware and software costs. This leaves more budget for research and development, new technology, and growth.
How else are cloud communications helping manufacturers thrive?
1. Ability to Solve Problems Fast
With cloud communications tools such as unified communications as a service (UCaaS), your entire team can access real-time updates on shipping delays, back-ordered materials, or changes to a delivery schedule. This level of communication enables every decision-maker on the team to stay in the loop so employees can collaborate and problem-solve quickly.
2. Enables Teams to Stay Connected from Wherever
As we saw during the pandemic, to ensure business continuity, employees in all industries should have the flexibility to work remotely. That way, when the unexpected happens, whether it’s a hurricane, a power outage, or a pandemic, there’s always someone available to take calls from customers and to keep things moving along with suppliers.
3. Frictionless Scaling
With cloud-based communications tools, your company doesn’t need to purchase new hardware or software to expand your capabilities. The technology grows with you. Adding new users to your communications platform can be as simple as making the change remotely from the software’s control panel.
4. Easier to Leverage Data
With cloud technology, manufacturers have access to data that reveals insights at each supply chain and value chain point. When you and your teams have vast amounts of valuable data at your fingertips, taking action based on discovered patterns and trends happens in real-time.
5. Breaks Down Silos
With UCaaS, all of your communication tools are available from one app. This makes it easier to keep track of conversations and to collaborate in larger groups without creating confusion. You can also centralize the management of the entire company through one platform.
6. Better Reliability and Security
With cloud communications, your cloud provider hosts the software and the communications system off-site in a protected data center. With a reliable, security-first cloud communications system, your teams can count on flawless communication whether you’re coordinating with suppliers or sharing data internally.
Yeo & Yeo Technology’s cloud-based VoIP phone system and collaboration platform, YeoVoice powered by Elevate, is a powerful solution for manufacturers. Learn more about YeoVoice on our website or contact us.
Information used in this article was provided by our partners at Intermedia.
Modern businesses thrive when they master communications. To do this, they need the right technology. Traditional legacy phone systems are restrictive and limited, but moving phone communications to the cloud enables mobility and flexibility. If you’re considering upgrading your phone system, you’ll want to know about a PBX cloud phone system.
What Are PBX Cloud Phones?
PBX stands for a Private Branch Exchange. PBX phones have been around for some time, and they create a private telephone network within one organization. In a standard PBX, the ability to use the system is only on-premises. Such a setup requires expensive servers on-site.
What’s different about PBX cloud phones is that they use VoIP (voice over internet protocol), which means they don’t need phone lines, only an internet connection. A cloud PBX lives in the cloud, sitting in a secure and remote data center. You still have all the same features for routing and management, just without the costly equipment.
How Do PBX Phone Systems Work?
As noted, the internet is the basis of cloud PBX platforms, not phone lines. With a connection, users can make and receive calls in many ways. You can use a desk phone that plugs into a router, similar to conventional PBX phones. Additionally, you can use an application on your desktop or mobile phone. Using cloud-based phones offers true versatility to take and place calls from wherever, which means they are ideal for remote or hybrid work.
The application itself and the data acquired from usage (i.e., voicemails) reside in the cloud. To leverage such a solution, you’ll engage with a provider that delivers the software and hardware. It simplifies phone system billing and management.
Why Move Phone Systems to the Cloud?
In the past year, businesses experienced tremendous change due to the pandemic. Remote work became the norm; however, this was a trend already in the making. COVID-19 accelerated it. This shift caused many companies to rethink their internal and external communications and migrate everything to the cloud.
Converting to the cloud for applications across the enterprise offers freedom from a centralized work location. While the return to the office is already occurring, that doesn’t mean you still don’t need to provide flexibility to your team regarding communications.
When you move to the cloud, you can have confidence that it’s secure, cost-effective, and scalable.
Ready to upgrade your phone system? Contact us today to discuss how the cloud can support your growing business.
Information used in this article was provided by our partners at Intermedia.
I’ve noticed a new administrator on my network but don’t know who it is.
If you’ve checked around the business and no one has created the new administrator account, speak to your IT support partner immediately. This may be a sign that you have an intruder in your network waiting to launch an attack.
A really important document has disappeared from my network. Can I get it back?
Hopefully, you have a working daily or continuous backup in place? If so, it’s simply a case of retrieving a copy of your document. If you don’t have a backup, then it may be trickier. First, you may want to establish how the file has disappeared. A good IT support partner should be able to guide you through this (also, get them to sort out your backup).
Teams notifications are distracting me from my work. Can I stop them?
Yep, just turn them off! You can set your status to Do Not Disturb, which will stop anything bothering you. Alternatively, you can now make yourself invisible by appearing offline when you want to get your head down and work.
The threat landscape continues to evolve and expand rapidly. As attack vectors multiply, from endpoints to networks to the cloud, many enterprises address each vector with a best-in-class solution to protect those specific vulnerabilities. However, these point tools don’t connect the dots across the entire technology stack. As a result, security data is collected and analyzed in isolation, without any context or correlation, creating gaps in what security teams can see and detect.
Extended Detection and Response (XDR)
Extended Detection and Response (XDR) is the evolution of Endpoint Detection and Response (EDR). XDR automatically collects and correlates data across multiple security vectors, facilitating faster threat detection so that security analysts can respond quickly before the scope of the threat broadens. In short, XDR extends beyond the endpoint to make decisions based on data from more products and can act across your stack by acting on email, network, identity, and beyond.
As XDR is gaining traction and emerging as a critical next-generation security tool, here are five questions you should consider while looking at an XDR solution.
1. Does the XDR Solution Provide Rich, Cross-Stack Visibility with the Ability to Seamlessly Ingest from Multiple Data Sources?
A robust XDR platform enables enterprises to seamlessly ingest structured, unstructured, and semi-structured data in real-time from any technology product or platform, breaking down data silos and eliminating critical blind spots.
2. Does the XDR Solution Provide Automated Context and Correlation Across the Different Security Layers?
Many EDR solutions require (human) security teams to conduct investigations. But given the volume of alerts generated, many security teams are not resourced to dwell into every incident. A robust XDR solution should be augmented with AI and automated built-in context and correlation.
3. Does the XDR Solution Auto-Enrich Threats with Integrated Threat Intelligence?
As new threats emerge, a lack of external context makes it difficult for analysts to determine whether an alert or indicator represents a real threat to their organization. Threat intelligence provides up-to-date information on threats, vulnerabilities, and malicious indicators freeing security teams to focus on what is most important. A well-built XDR solution enables threat intelligence integration from multiple sources to help security teams prioritize and triage alerts quickly and efficiently.
4. Does the XDR Solution Automate Response Across Different Domains?
Of course, incident detection and investigation need to trigger an effective response to mitigate the incident. The response needs to be pre-defined and repeatable to make remediation more efficient and intervene at any step in an attack that is in progress. The response should distinctively define both short-term and long-term measures that can be used to neutralize the attack. It is also essential to understand the cause of the threat to improve security and prevent attacks of a similar manner in the future. All necessary steps must be taken to ensure that similar attacks are not likely to happen again.
5. Does the XDR Solution Let You Easily Integrate with Leading SOAR Tools?
As you may have other security tools and technologies deployed in your SOC, your XDR solution should let you utilize your existing investments in security tools. Key features would be built-in integrations, including automated responses and integrated threat intelligence.
XDR is the Future of EDR
Specialized security products must work together to defend against an intensifying effort to overrun the digital barriers that protect our now technology-dependent lives. As with any new technology entering the marketplace, there is a lot of hype, and buyers need to be wise. The reality is, not all XDR solutions are alike. YeoDefense, powered by SentinelOne, unifies and extends detection and response capability across multiple security layers, providing security teams with centralized end-to-end enterprise visibility, powerful analytics, and automated response across the complete technology stack.
If you would like to learn more about YeoDefense, contact us.
Information used in this article was provided by our partners at SentinelOne.
In the past, to configure security policies, teams were required to use group policies, System Center Configuration Manager, or Microsoft Endpoint Manager. Essentially, they were using the IT management tool to set up and maintain security. Therefore, even when an organization had security administrators, they depended on the IT team for any required change.
Today’s Security Challenges Require a Different Approach
While it might have worked in the past to have the IT team manage security controls, modern enterprises are at the stage where that is no longer scalable. Today, we aren’t just configuring a legacy antivirus and a password policy. We need to consider different attack surfaces and tune our preventative controls accordingly. The time when a security administrator could raise an IT ticket and then sit and wait is long behind us.
How Can an Organization Improve Its Cybersecurity?
1. Implement Role-Based-Access-Control (RBAC)
The security team deals with a lot of sensitive information. Therefore, the principle of least privilege is critical. The bottom line is that only people with an apparent business reason should have access to specific information. For example, security administrators should see the endpoint configuration, manage agent update cycles, and configure device policies and the firewall. Still, they may not need access to forensic capabilities or access to active incidents. With Role-Based-Access-Control (RBAC), this can be achieved.
2. Lock Down the Network and Devices
Reducing the attack surface is a critical task for security administrators. Often, the first step is to configure device restriction policies and the firewall. Consider who should have access to information and whether that access should be restricted to read-only. When managing firewalls, also consider:
- if rules should apply across Windows, macOS, and Linux
- if there should be an Allow or Block rule
- if rules should apply for a specific protocol, port, application, etc.
3. Consider an XDR Security Solution
Extended Detection and Response (XDR) Security solutions monitor an organization’s entire infrastructure, including endpoints, the cloud, mobile devices, and more. These systems actively search and respond to threats in real-time to protect organizations from advanced cyberattacks.
The increasing complexity in today’s threat landscape makes it clear that waiting several days to make a change to preventative controls is no longer acceptable. Security technologies have evolved and provided integrated security management capabilities that empower security administrators to make informed risk-based decisions.
YeoDefense XDR, powered by SentinelOne, provides integrated security management capabilities that are truly designed for enterprises. Businesses benefit from multi-tenancy and Role-Based-Access-Control (RBAC), which enable the principle of least privilege. If the security administrator needs to configure a device restriction policy or firewall rules, or optimize Endpoint Platform Protection (EPP) or Endpoint Detection and Response (EDR) controls, they can do that all within the SentinelOne management console in just a few clicks.
If you would like to learn more about how YeoDefense can help secure your organization, Contact Yeo & Yeo Technology.
Information used in this article was provided by our partners at SentinelOne.
Stop Hackers from Stealing Your Data
When you think about it, the very nature of email makes it the weakest point of any security setup. For many of us, it’s both our greatest tool and most hated nemesis.
You have lots of staff, accepting hundreds of emails every day. And even the best email filters in the world can’t stop clever hackers because they’re constantly inventing new ways to get in.
All they need is one member of your staff to click one dodgy link. And that can give hackers enough access to start monitoring what the business is doing. From there, they can spot ways to access business funds.
In this eBook, we will follow the story of a business that was compromised by an email attack and explore ways that the attack could have been prevented.
We discuss:
- Common Email Scams and Hacks
- 9 Layers of Email Security You Can Implement
- Moving Forward After an Attack
If your business isn’t yet fully protected with the correct layers of security for your specific situation, Yeo & Yeo Technology can help.